June 23, 2023 • 7 min read
Six Best Practices When Preparing for Third-Party Audits

Will Cryer
Depending on your business’s size, industry, and compliance needs, it will be subject to third-party audits. Businesses will typically choose to undergo a third-party audit with the goal of achieving or maintaining a security certification, such as SOC 2 (I and II), ISO, or PCI DSS.
While these audits are time-intensive, obtaining certifications are one of the most effective ways to provide assurance to prospective customers that your business adheres to industry-level security standards.
AuditBoard’s new ebook, The InfoSec Survival Guide: Achieving Continuous Compliance, examines how organizations can simultaneously prepare for third-party audits while incorporating continuous monitoring practices into their InfoSec compliance program. Download the full guide here, and continue reading below for six best practices to follow when preparing for third-party audits.
Six Best Practices When Preparing for Third-Party Audits
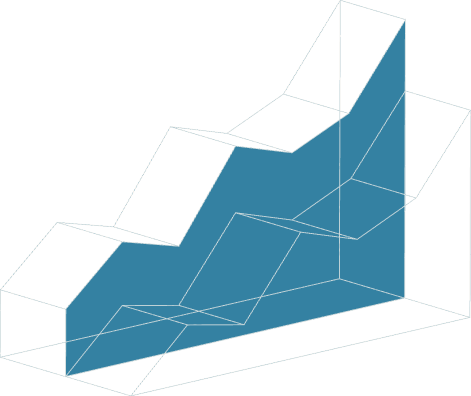
Given the time-intensiveness of preparing for third-party audits as well as their frequency, one of the most common challenges is time management. Internal teams with already full plates that are not sufficiently prepared for what is coming will wind up taking each audit request as it comes. As a result, as each new request rolls in, they are unable to build their compliance activities out in a scalable and sustainable manner.
- SOC 2 Type I
May take 3-4 months to complete
Period of coverage is 12 months - May take 3-4 months to complete
- Period of coverage is 12 months
- SOC 2 Type II
May take 2-3 months to complete
Period of coverage is 12 months - May take 2-3 months to complete
- Period of coverage is 12 months
- PCI DSS
May take 6 months to complete
Period of coverage is 12 months - May take 6 months to complete
- Period of coverage is 12 months
- ISO 27001
May take 3-6 months to complete
Period of coverage is 3 years - May take 3-6 months to complete
- Period of coverage is 3 years
Selecting a baseline controls framework that meets multiple requirements across frameworks is one way to enable your organization to achieve its compliance objectives more efficiently. The following are additional best practices InfoSec teams can act upon to be well-prepared in advance for third-party audits.
- Understand and clearly define the scope of the third-party audit. Many frameworks require a risk assessment over the subject matter in question in order to set the scope of a report. Look at the guidance provided by the governing body for the chosen compliance framework. Not only will this help determine what your initial steps should be, but it is also essential for setting and communicating timelines and deadlines. Be sure to loop in your internal stakeholders early on and communicate to them the purpose and objectives of the audit.
- Prepare your internal stakeholders for what they will be responsible for. Take the time to debrief your stakeholders on the purpose and goals of the audit, and to clearly outline the scope involving them. Be sure to share due dates and timelines well in advance. Define processes in a way that are scalable, as nothing exists in a vacuum from a compliance perspective.
- Collect evidence early on. This allows you to get a pulse on the environment well in advance to eliminate surprises. Being able to self-identify and communicate issues you are already aware of is advantageous to early remediation. If available, review audit and compliance projects that have already occurred that year to leverage any evidence or areas of overlap. This can help prevent duplicate requests and questions to stakeholders.
- Get the right level of executive leadership involved. Educate management on why the audit is taking place and when/where they will need to step in to get additional support for ensuring things are done timely. Agree to these protocols in advance so you can rely on their push when the time is needed.
- Be familiar with the scope of your certifications and reports. If you have a SOC report but are getting questions from customers that are not related to the report – make sure you are tracking this data. Doing so will allow you to address these areas in the scope of your SOC report for next year, and you will be better prepared to answer those questions next year.
- Establish a good relationship with the external audit team. Set communication expectations early on and agree to protocols for communicating potential issues, how they will be communicated, format of communication, etc. The more you can hold your external auditors accountable to pre-discussed protocols, the less likely there will be surprises in the audit cycle.
If your business has taken a risk-based, continuous approach to compliance throughout the year, it is likely that it will have been preparing for its third-party audits throughout the course of its day-to-day compliance activities. To learn more about how you can incorporate continuous monitoring throughout your InfoSec compliance program, download the full ebook, The InfoSec Survival Guide: Achieving Continuous Compliance.
About the authors

Will Cryer, CISA, CIPT, is an Area Director of Commercial Sales at AuditBoard. Prior to joining AuditBoard, Will spent 9 years with EY in Denver specializing in information technology audits, SOX/ICFR, cybersecurity, privacy, ISO 27001, and SOC Reporting across the FinTech, Technology, and Real Estate industries. Connect with Will on LinkedIn.
You may also like to read


Mind your business: The real secret to career growth

How to transform your GRC strategy with AI-driven tools

How AI maturity impacts risk, speed, and strategy

Mind your business: The real secret to career growth

How to transform your GRC strategy with AI-driven tools
Discover why industry leaders choose AuditBoard
SCHEDULE A DEMO