April 22, 2024 • 21 min read
The Definitive Guide to the ISO 27001 Audit

Christina Chabot-Olson
The ISO/IEC 27001 (ISO 27001) certification journey consists of several internal and external audits and assessments along the way. The standard is optional and companies that choose to implement ISO 27001 also have the choice to pursue certification. Choosing to undergo certification has several benefits as outlined below. Regardless of the certification choice, ISO 27001 implementation typically involves the same high-level steps and involves creating and maintaining certain required processes and documents. Preparation is key and automation can efficiently and effectively facilitate these efforts.
What is an ISO 27001 Audit?
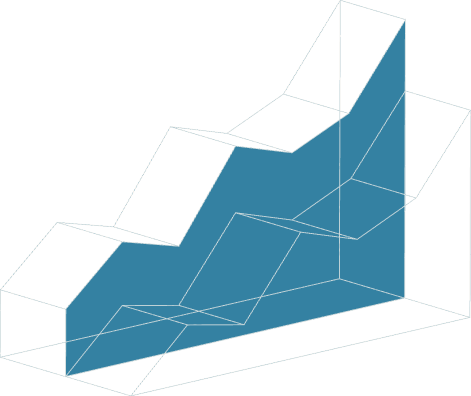
ISO 27001 audit involves implementing the standard, conducting audits, remediating nonconformities, and optionally pursuing certification.
The Standard
ISO 27001 is a widely acknowledged ISO standard that defines best practices for Information Security Management Systems (ISMS). The standard is governed by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC). ISO 27001 is one of several in the broader ISO/IEC 27000 series of standards that collectively focus on information security. The requirements set forth by ISO 27001 enable organizations to effectively manage information security-related activities in support of cybersecurity activities.
Applicable to businesses of any size or industry, ISO 27001 aids organizations in demonstrating a commitment to the highest levels of data security and privacy. By adhering to these standards, companies can boost their brand reputation and foster trust among both internal stakeholders and external parties.
The most up-to-date standard was updated in 2022. Organizations must recertify against the 2022 version of the standard no later than October 31, 2025, to continue their ISO certification.
Audit and Reviews
The ISO 27001 certification process consists of several types of audits, including Internal and external audits. All audits should be governed by an audit program and audit plan. The lead auditor is responsible for developing the audit plan and may be assisted by audit team members during audit execution depending on the audit scope. The number of effective personnel within the ISMS scope and the complexity of organizational processes are the key factors in determining the ISMS audit length (in terms of audit days).
Because of the COVID-19 pandemic, most ISO 27001 audits were performed remotely from 2020 through 2023. Starting 2024, audits will occur on-site with remote audits being an option with appropriate justification.
Internal Audit
Clause 9.2 of the standard mandates that organizations conduct internal audits at planned intervals to determine compliance with the requirements of the standard. Internal audits should be governed by a formal internal audit process.
Businesses can employ their own internal auditors or retain third-party companies or contractors to conduct the internal audit, if, for example, the organization lacks the resources to perform the internal audit. The key requirement in the selection of an internal auditor is independence, meaning the internal auditor should be independent of the function being audited.
Management Review
ISO 27001 Clause 9.3 mandates management review. ISMS Management Review must occur at planned intervals to ensure continuing suitability, adequacy, and effectiveness.
External Audits
Stage 1 and Stage 2, Surveillance, and Recertification audits are considered external audits, performed by external auditors. External audits are also referred to as third-party audits. In some cases, external audits may also be carried out by interested parties.
Stage 1 Audit
Although not required, organizations may conduct a gap analysis to ascertain the ISMS implementation status prior to proceeding to a Stage 1 audit. A Stage 1 audit is essentially a documentation review to ensure the required documentation is in place for an operational ISMS. The purpose of a Stage 1 audit is to gauge an organization’s readiness for an ISO 27001 certification.
Stage 2 Audit
Stage 2 audits focus on the implementation and effectiveness of an organization’s information security controls, as well as its compliance with ISO 27001 requirements. Stage 2 can be viewed as the initial certification audit.
Surveillance Audits
Surveillance audits occur annually between Stage 2 and Recertification audits. The purpose of these audits is to validate continued operational compliance and continual improvement of the ISMS. All requirements of the standard must be audited between the two Surveillance audits.
Recertification Audit
Recertification audits are essentially another Stage 2 audit where all requirements of the standard are assessed to gauge ISMS compliance with the standard. Recertification audits occur every three years at the end of the certification cycle. After recertification, the ISMS is certified again for three years.
Nonconformities and Opportunities for Improvement
Nonconformities refer to instances where the management system does not meet the requirements specified in the standard. Nonconformities can arise from various sources such as internal audits, external audits, management reviews, or incident investigations. Nonconformities can be related to processes, documentation, controls, or any other aspect of the ISMS. Nonconformities are classified typically as either major or minor:
Major Nonconformities consist of:
- The absence or total breakdown of a system.
- A situation that raises significant doubt that products or services will meet specified requirements.
- A group of Minor nonconformities against one requirement can represent a total breakdown of the system, and thus be considered a major nonconformity.
Minor Nonconformities include:
- A lapse of either discipline or control during the implementation of system/procedural requirements does not indicate a system breakdown or raise doubt that products or services will meet requirements. The overall system requirement is defined, implemented, and effective.
Opportunities for Improvement (OFIs) are elements or processes within the ISMS that:
- Are not nonconformities but could be enhanced to add value to the organization, increase the effectiveness or efficiency of the ISMS, or further reduce security risks.
Addressing ISO 27001 nonconformities is crucial for maintaining the integrity and effectiveness of the ISMS. Organizations should remediate nonconformities promptly and effectively. Remediation involves taking corrective and preventive actions to eliminate the causes of the nonconformities and prevent their recurrence. Identification and correction of nonconformities are integral to the continuous improvement aspect of ISO 27001.
Accreditation and Certification Bodies
ISO 27001 certificates are issued by certification bodies. An accreditation body accredits a certification body. There are numerous ISO accreditation bodies worldwide. For instance:
- In the United States, the primary ISO accreditation body is the ANSI National Accreditation Board (ANAB).
- In Canada, it is the Standards Council of Canada (SCC).
- In the European Union (EU), accreditation bodies for conformity assessment are typically organized at the national level. For example, in Germany, the accreditation body is the Deutsche Akkreditierungsstelle GmbH (DAkkS), and in the United Kingdom, it is the United Kingdom Accreditation Service (UKAS).
Currently, there are 38 ANAB-accredited ISO/IEC 27001 certification bodies. These accredited certification bodies undergo continuous audits from accreditation bodies throughout the year.
Why is ISO 27001 Important?
ISO 27001 certification provides assurance to stakeholders, customers, and partners that the organization has implemented robust information security measures, potentially enhancing trust and credibility. Undergoing the ISO 27001 certification process has the following additional benefits:
- By obtaining an ISO 27001 certification, organizations can showcase their dedication to protecting sensitive information and ensuring its availability, confidentiality, and integrity.
- ISO 27001 certification is recognized globally, providing assurance to stakeholders that an organization’s information security practices are in line with international standards.
- By obtaining an ISO 27001 certification, organizations can differentiate themselves from competitors and attract new business.
- Identifying potential weaknesses and providing recommendations for improvement.
- Organizations can demonstrate compliance with legal and compliance requirements.
- Implementing the controls outlined in ISO 27001 can help mitigate the risk of data breaches and cyber-attacks, protecting an organization’s reputation and minimizing financial losses.
How Does ISO 27001 Work?
ISO 27001 works by providing a framework for establishing, implementing, maintaining, and continually improving ISMS. The standard revolves around a risk-based approach to information security, and it’s structured as follows:
- Risk Assessment and Treatment: ISO 27001 requires organizations to assess information security risks, considering threats, vulnerabilities, and impacts, and then implement appropriate security controls to mitigate these risks. Once risks have been identified, the organization must decide on how to manage or treat these risks. Common risk treatment options are to:
- Apply controls to mitigate the risk.
- Accept the risk if it falls within the organization’s risk appetite.
- Transfer the risk, possibly through insurance.
- Avoid the risk by not performing activities that produce the risk.
- Control Implementation (Annex A): To mitigate risks, ISO 27001 includes Annex A, which provides a set of controls divided into categories. ISO 27001:2013 Annex A consists of 114 controls in 14 domains, 27001:2022 Annex A contains 93 controls grouped into four categories. These controls are not mandatory; an organization needs to implement only those deemed necessary following the risk assessment process. Controls range from technical solutions to management processes and are laid out as follows:
ISO/IEC 27001:2013 Annex A Control Domains
- A5 – Information security policies (2 Controls)
- A6 – Organization of information security (7 Controls)
- A7 – Human resource security (6 Controls)
- A8 – Asset management (10 Controls)
- A9 – Access control (14 Controls)
- A10 – Cryptography (2 Controls)
- A11 – Physical and environmental security (15 Controls)
- A12 – Operations security (14 Controls)
- A13 – Communications security (7 Controls)
- A14 – System acquisition, development, and maintenance (13 Controls)
- A15 – Supplier relationships (5 Controls)
- A16 – Information security incident management (7 Controls)
- A17 – Information security aspects of business continuity management (4 Controls)
- A18 – Compliance (8 Controls)
ISO/IEC 27001:2022 Annex A Control Categories
- Organizational (37 Controls)
- People (8 Controls)
- Physical (14 Controls)
- Technological (34 Controls)
ISO/IEC 27001:2022 Annex A Explained
- ISMS Documentation: ISO 27001 requires that organizations document their ISMS and its processes, including the scope of the ISMS, risk assessment and treatment methodology, Statement of Applicability (which details which controls from Annex A have been applied), risk treatment plan, and various policies and procedures.
- Continual Improvement: ISO 27001 requires organizations to adopt a continuous improvement approach, leveraging audits, management reviews, and the monitoring of ISMS processes to evolve the system over time to ensure its effectiveness and relevance.
- Certification: While not mandatory, many organizations choose to undergo certification by an accredited certification body to demonstrate their compliance with the standard. This involves an external audit by the certification body.
How to Prepare for an ISO 27001 Certification Audit
Audit preparation includes Identifying the processes to be audited, gathering required documentation, and providing training to employees and contractors.
Identifying the key processes to be audited
Key processes are those related to critical information assets, processes that involve high levels of risk or processes essential for the functioning of the ISMS. Identifying key processes starts by clearly defining the ISMS scope. In defining the scope, the organization should consider the ISMS boundaries, locations, and in-scope functions. Risk assessment results and legal and regulatory requirements can also be used to identify and prioritize key processes.
After process identification, conversations with process owners and key stakeholders should occur to understand process criticality, complexity, and impact on the ISMS.
The goal of identifying key processes is to ensure that the processes are implemented and operational.
Gather the required documents for the audit report
The standard calls for both required and optional documented information. For example, ISO 27001:2013:
- Clause 4.3 requires that the scope is documented information.
- Clause 5.2 requires a documented information security policy.
- Clause 6.1.2 requires the retention of documented information about the information security risk assessment process.
- Clause 6.1.3 requires the retention of documented information about the information security risk treatment process.
Additional ISO 27001:2013 required and recommended documented information are listed below.
Required Information Security Documented Information
- Results of risk assessments/evaluations
- Risk Treatment Plans
- Information security roles and responsibilities
- Inventory of assets
- Rules for acceptable use of assets
- Information Classification scheme
- Access Control Policy
- Operating procedures for IT management
- Logs – user activities, exceptions, security events
- Secure system engineering principles (if applicable)
- Incident management procedure
- Business and information security continuity plans/procedures
- Statutory, regulatory, and contractual requirements (Compliance obligations)
Recommended Information Security Documented Information
- Mobile Device Policy
- Telework Policy (Remote Work Policy)
- Clear Desk / Clear Screen Policy
- Backup (data) routines/schedules
- Evidence of backup restoration testing
- Evidence of business and information security continuity testing
- Change Management policy or procedures
- Information security in supplier agreements
The standard also mandates required information related to specific processes. Clause 9.2 requires the retention of documented information as evidence of the audit program(s) and the audit results. Clause 9.3 requires the same regarding management review. Clause 10.1 states that the organization shall retain documented information as evidence of the nature of corrective actions and the results of corrective actions.
All required documented information should be readily available in audits.
Provide training to the necessary personnel and contractors
ISO/IEC 27001:2013 clause 7.2 requires organizations to ensure persons are competent based on appropriate education, training, or experience. Annex A control A.7.2.2 requires appropriate awareness education and training and regular updates in organizational policies and procedures, as relevant for their job function for all employees of the organization and, where relevant, contractors.
How Automation Leads to Compliance
Establishing, maintaining, and continually improving an information security management system that aligns with ISO 27001 can present significant challenges. Implementing the appropriate technology can greatly enhance the process of achieving ISO 27001 compliance. With AuditBoard’s CrossComply, your team can expedite compliance actions and workflows, including those related to maintaining your organization’s ISO 27001 compliance activities.
CrossComply allows you to integrate your organization’s tech stack to automate IT risk and compliance workflows. The tool facilitates importing multiple frameworks to enable automatic requirements mappings. CrossComply also leads to streamlining reporting in support of business strategy.
Frequently Asked Questions About ISO/IEC 27001
What is an ISO 27001 audit?
The ISO 27001 certification process consists of several types of audits, including internal and external audits. All audits should be governed by an audit program and audit plan. The lead auditor is responsible for developing the audit plan. Internal audits include a formal internal audit and management review. External audits include Stage 1 and Stage 2, Surveillance, and Recertification audits. Nonconformities refer to instances where the management system does not meet the requirements specified in the standard. Addressing ISO 27001 nonconformities is crucial for maintaining the integrity and effectiveness of the ISMS. Organizations should remediate nonconformities promptly and effectively.
Why is the ISO 27001 audit important?
ISO 27001 certification provides assurance to stakeholders, customers, and partners that the organization has implemented robust information security measures, potentially enhancing trust and credibility.
How does ISO 27001 work?
ISO 27001 enables a risk-based approach to information security and risk management. The process starts with assessing and treating risk items. Selecting applicable Annex A controls to mitigate risk items is next. The standard requires certain documented information. Organizations can engage a certification body to pursue certification after meeting the requirements, implementing controls, and conducting internal audits and management reviews.
About the authors

Christina Chabot-Olson, CPA, CISA, is a Senior Manager of Product Solutions at AuditBoard. Christina has 10 years of experience in public accounting and industry specializing in financial accounting, Sarbanes-Oxley compliance, internal and external auditing, SOC reporting, and financial software implementations. Connect with Christina on LinkedIn.
You may also like to read


Mind your business: The real secret to career growth

How to transform your GRC strategy with AI-driven tools

How AI maturity impacts risk, speed, and strategy

Mind your business: The real secret to career growth

How to transform your GRC strategy with AI-driven tools
Discover why industry leaders choose AuditBoard
SCHEDULE A DEMO